Overview: Where we are and What Is Still Missing In the previous part of this series, we made our fake secure channel much less fake. We started with the broken encrypted transport from Part 1, added integrity with HMAC, added sequence numbers to make the record layer less naive, and then moved to AEAD — the approach modern systems usually use to protect records. At that point, our protocol coul
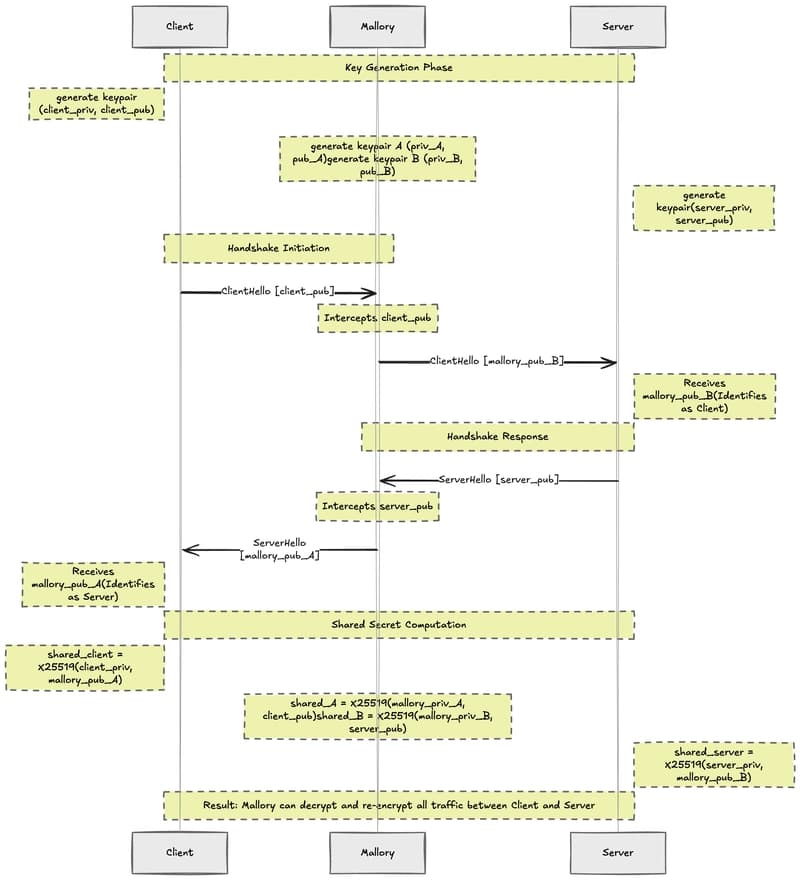
Rebuilding TLS, Part 3 — Building Our First Handshake
Dmytro Huz·Dev.to··1 min read
D
Continue reading on Dev.to
This article was sourced from Dev.to's RSS feed. Visit the original for the complete story.