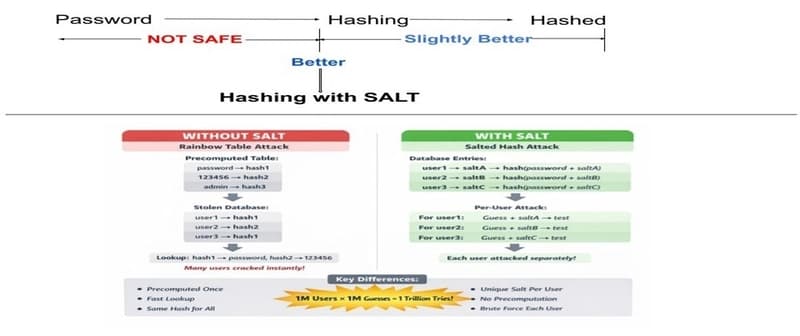
What if I told you that even if you hash passwords, an attacker might still crack them in seconds? Authentication is one of the most critical parts of any application—and also one of the most misunderstood. In this post, we’ll think like an attacker, break insecure implementations using Java examples, and then progressively strengthen our defenses using hashing and salting. If you’ve ever stored a
Authentication Security Deep Dive: From Brute Force to Salted Hashing (With Java Examples)
Sanjay Ghosh·Dev.to··1 min read
D
Continue reading on Dev.to
This article was sourced from Dev.to's RSS feed. Visit the original for the complete story.