Block 99% of malicious injections with just 3 lines of code — PoC inside. Let’s talk about the elephant in the Web3 room. When the recent Drift Protocol vulnerability exposed hundreds of millions in potential risk because of a single validation edge case, the entire industry felt a collective chill. But here’s the terrifying truth most developers are still ignoring: If deterministic, battle-teste
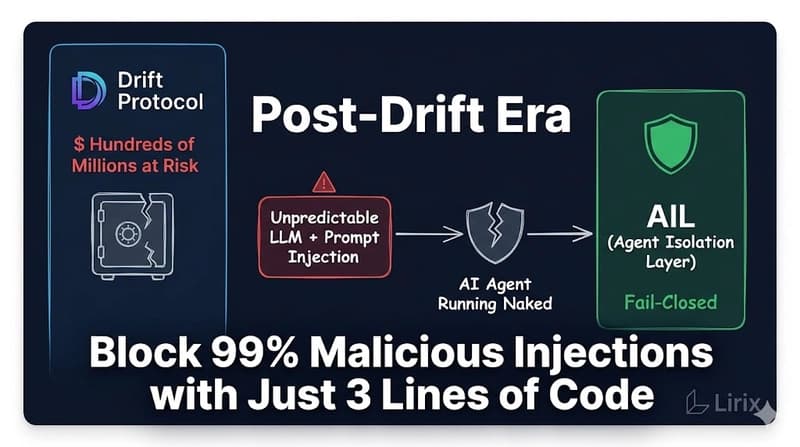
How Expensive is a Naked AI Agent? The $285M Tragedy & The Inevitability of AIL Architecture
lokii·Dev.to··1 min read
D
Continue reading on Dev.to
This article was sourced from Dev.to's RSS feed. Visit the original for the complete story.